Top 10 Benefits of Application Performance Monitoring
In our digital world, if your apps go down, you're out of business. Being able to…
READ MORE
In our digital world, if your apps go down, you're out of business. Being able to…
READ MORE
Today, every home and business is dependent on devices. These devices need a way of…
READ MORE
Cloud computing security is the processes and necessary technologies that protect cloud computing architectures against…
READ MORE
You have no idea how close to the future we are. Trust us. Companies across…
READ MORE
Technology is evolving at a pace we can barely keep up with. The internet, computers,…
READ MORE
Did you know that every 39 seconds on average, hackers target computers with an Internet…
READ MORE
While there are many definitions of hybrid cloud architecture, the most basic definition is a…
READ MORE
A public cloud uses the standard cloud computing framework to create services that are then…
READ MORE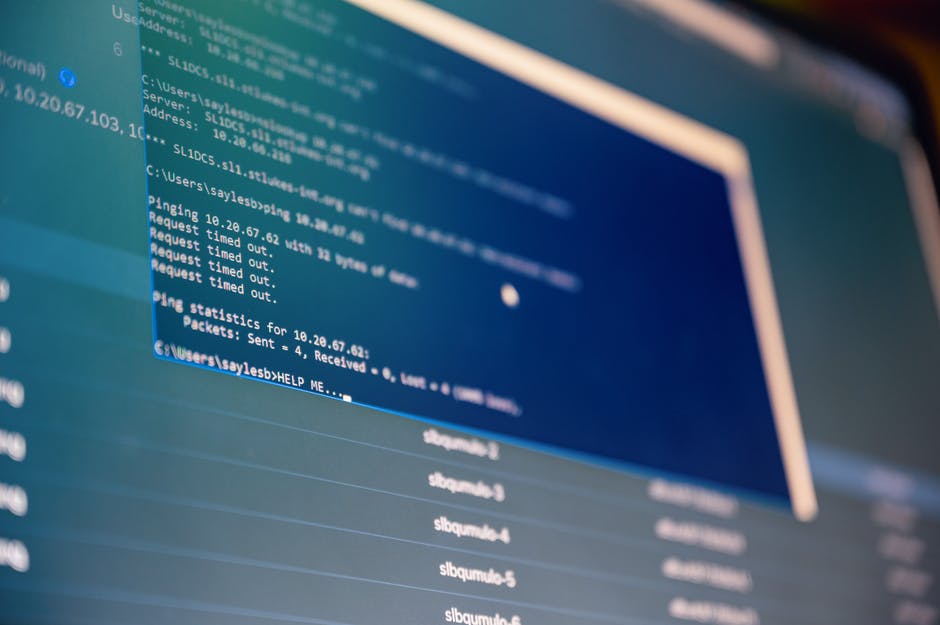
How many different software platforms and apps does your team use? Chances are it's a…
READ MORE
Data is the driving force of the business world today. Advanced technologies like AI, machine…
READ MORE
A Security Operation Center, or SOC, is a facility responsible for monitoring an organization's IT…
READ MORE